-
Posts
2,544 -
Joined
-
Last visited
Posts posted by trium
-
-
karat - über sieben brücken musst du gehn (gdr 1979)
-
puhdys - alt wie ein baum (gdr 1976)
-
puhdys - wenn ein mensch lebt (gdr 1973)
-
karat - schwanenkönig (gdr 1980)
-
matthias reim - eiskalt
-
holger biege - sagte mal ein dichter (1978 - gdr)
-
karussel - als ich fortging (1987 - gdr)
-
karat - hab den mond mit der hand berührt (in the 80s - gdr)
-
maywood - late at night
-
ublock v1.52.0
github-actions released this
08. sept 2023
Fixes / changes
-
Add
json-prune-xhr-responseandtrusted-replace-xhr-responsescriptlets -
Use
globalThisinstead ofselfin scriptlet helper -
Add
json-prune-fetch-responsescriptlet - Position reload icon in logger as per feedback
-
Re-factor extra args for
set-constantscriptlet - Use Unicode version of hostnames in element picker
- Disallow trailing CSS universal selector unless properly separated
-
Fix/improve
xml-prunescriptlet - Put uBO's icon in nav bar by default
- Properly serialize CSS combinators according to position in selector
-
Improve
no-xhr-ifscriptlet - Use non-normalized URL for reload/report operations
-
Add commented keywords to
googlesyndication_adsbygoogle.jsscriptlet -
Improve
fingerprint2.jsscriptlet - Nothing can come after action operator in procedural cosmetic filters
-
Add
trusted-replace-fetch-responsescriptlet -
Harden
spoof-cssscriptlet - Support negated pattern for stack test in scriptlets
- Fix looking up clickable URLs in code viewer
-
Fine tune logging capabilities of
json-prunescriptlet -
Add
stackNeedleargument tojson-prunescriptlet -
Improve
remove-classbehavior - Add visual hint for filtered out rows in firewall pane
-
Add
$currentISODate$totrusted-set-local-storage-itemscriptlet -
Eliminate case-sensitivity from values in
set-cookiescriptlet
-
Add
-
ff v115.2.1 esr
12. sep 2023
Fixed
QuoteSecurity Vulnerability fixed in Firefox 117.0.1, Firefox ESR 115.2.1, Firefox ESR 102.15.1, Thunderbird 102.15.1, and Thunderbird 115.2.2
- Announced September 12, 2023
- Impact critical
- Products Firefox, Firefox ESR, Thunderbird
- Fixed in
-
- Firefox 117.0.1
- Firefox ESR 102.15.1
- Firefox ESR 115.2.1
- Thunderbird 102.15.1
- Thunderbird 115.2.2
#CVE-2023-4863: Heap buffer overflow in libwebp
- Reporter Apple Security Engineering and Architecture (SEAR) and The Citizen Lab at The University of Toronto's Munk School
- Impact critical
Description
Opening a malicious WebP image could lead to a heap buffer overflow in the content process. We are aware of this issue being exploited in other products in the wild.
References
-
ff v102.15.1 esr
12. sep 2023
Fixed
QuoteSecurity Vulnerability fixed in Firefox 117.0.1, Firefox ESR 115.2.1, Firefox ESR 102.15.1, Thunderbird 102.15.1, and Thunderbird 115.2.2
- Announced September 12, 2023
- Impact critical
- Products Firefox, Firefox ESR, Thunderbird
- Fixed in
-
- Firefox 117.0.1
- Firefox ESR 102.15.1
- Firefox ESR 115.2.1
- Thunderbird 102.15.1
- Thunderbird 115.2.2
#CVE-2023-4863: Heap buffer overflow in libwebp
- Reporter Apple Security Engineering and Architecture (SEAR) and The Citizen Lab at The University of Toronto's Munk School
- Impact critical
Description
Opening a malicious WebP image could lead to a heap buffer overflow in the content process. We are aware of this issue being exploited in other products in the wild.
References
-
ff v117.0.1
12. sep 2023
Fixed
-
Fixed a bug causing links opened from outside Firefox to not open on macOS (bug 1850828)
-
Fixed a bug causing extensions using an event page for long-running tasks to be terminated while running, causing unexpected behavior changes (bug 1851373)
-
Temporarily reverted an intentional behavior change preventing Javascript from changing
URL.protocol(bug 1850954).
NOTE: This change is expected to ship in a later Firefox release alongside other web browsers and sites are encouraged to find alternate ways to change the protocol if needed. -
Fixed audio worklets not working for sites using WebAssembly exception handling (bug 1851468)
-
Fixed the
Reopen all tabsoption in theRecently closed tabsmenu sometimes failing to open all tabs (bug 1850856) -
Fixed the bookmarks menu sometimes remaining partially visible when minimizing Firefox (bug 1843700)
-
Fixed an issue causing incorrect time zones to be detected on some sites (bug 1848615)
-
-
ff v115.2.0 esr
29. aug 2023
Fixed
-
Various security fixes and other quality improvements.
QuoteSecurity Vulnerabilities fixed in Firefox ESR 115.2
- Announced August 29, 2023
- Impact high
- Products Firefox ESR
- Fixed in
-
- Firefox ESR 115.2
#CVE-2023-4573: Memory corruption in IPC CanvasTranslator
- Reporter sonakkbi
- Impact high
Description
When receiving rendering data over IPC
mStreamcould have been destroyed when initialized, which could have led to a use-after-free causing a potentially exploitable crash.References
#CVE-2023-4574: Memory corruption in IPC ColorPickerShownCallback
- Reporter sonakkbi
- Impact high
Description
When creating a callback over IPC for showing the Color Picker window, multiple of the same callbacks could have been created at a time and eventually all simultaneously destroyed as soon as one of the callbacks finished. This could have led to a use-after-free causing a potentially exploitable crash.
References
#CVE-2023-4575: Memory corruption in IPC FilePickerShownCallback
- Reporter sonakkbi
- Impact high
Description
When creating a callback over IPC for showing the File Picker window, multiple of the same callbacks could have been created at a time and eventually all simultaneously destroyed as soon as one of the callbacks finished. This could have led to a use-after-free causing a potentially exploitable crash.
References
#CVE-2023-4576: Integer Overflow in RecordedSourceSurfaceCreation
- Reporter fffvr
- Impact high
Description
On Windows, an integer overflow could occur in
RecordedSourceSurfaceCreationwhich resulted in a heap buffer overflow potentially leaking sensitive data that could have led to a sandbox escape.
This bug only affects Firefox on Windows. Other operating systems are unaffected.References
#CVE-2023-4577: Memory corruption in JIT UpdateRegExpStatics
- Reporter Lukas Bernhard
- Impact high
Description
When
UpdateRegExpStaticsattempted to accessinitialStringHeapit could already have been garbage collected prior to entering the function, which could potentially have led to an exploitable crash.References
#CVE-2023-4051: Full screen notification obscured by file open dialog
- Reporter Hafiizh
- Impact moderate
Description
A website could have obscured the full screen notification by using the file open dialog. This could have led to user confusion and possible spoofing attacks.
References
#CVE-2023-4578: Error reporting methods in SpiderMonkey could have triggered an Out of Memory Exception
- Reporter Irvan Kurniawan (@sourc7)
- Impact moderate
Description
When calling
JS::CheckRegExpSyntaxa Syntax Error could have been set which would end in callingconvertToRuntimeErrorAndClear. A path in the function could attempt to allocate memory when none is available which would have caused a newly created Out of Memory exception to be mishandled as a Syntax Error.References
#CVE-2023-4053: Full screen notification obscured by external program
- Reporter Umar Farooq
- Impact moderate
Description
A website could have obscured the full screen notification by using a URL with a scheme handled by an external program, such as a mailto URL. This could have led to user confusion and possible spoofing attacks.
References
#CVE-2023-4580: Push notifications saved to disk unencrypted
- Reporter Harveer Singh
- Impact moderate
Description
Push notifications stored on disk in private browsing mode were not being encrypted potentially allowing the leak of sensitive information.
References
#CVE-2023-4581: XLL file extensions were downloadable without warnings
- Reporter Umar Farooq (@Puf)
- Impact moderate
Description
Excel
.xlladd-in files did not have a blocklist entry in Firefox's executable blocklist which allowed them to be downloaded without any warning of their potential harm.References
#CVE-2023-4582: Buffer Overflow in WebGL glGetProgramiv
- Reporter Dohyun Lee (@l33d0hyun) of SSD-Disclosure Labs & DNSLab, Korea Univ.
- Impact low
Description
Due to large allocation checks in Angle for glsl shaders being too lenient a buffer overflow could have occured when allocating too much private shader memory on mac OS.
This bug only affects Firefox on macOS. Other operating systems are unaffected.References
#CVE-2023-4583: Browsing Context potentially not cleared when closing Private Window
- Reporter Thejaka Maldeniya
- Impact low
Description
When checking if the Browsing Context had been discarded in
HttpBaseChannel, if the load group was not available then it was assumed to have already been discarded which was not always the case for private channels after the private session had ended.References
#CVE-2023-4584: Memory safety bugs fixed in Firefox 117, Firefox ESR 102.15, Firefox ESR 115.2, Thunderbird 102.15, and Thunderbird 115.2
- Reporter Randell Jesup, Andrew McCreight, the Mozilla Fuzzing Team
- Impact high
Description
Memory safety bugs present in Firefox 116, Firefox ESR 102.14, Firefox ESR 115.1, Thunderbird 102.14, and Thunderbird 115.1. Some of these bugs showed evidence of memory corruption and we presume that with enough effort some of these could have been exploited to run arbitrary code.
References
#CVE-2023-4585: Memory safety bugs fixed in Firefox 117, Firefox ESR 115.2, and Thunderbird 115.2
- Reporter Donal Meehan, Sebastian Hengst, and the Mozilla Fuzzing Team
- Impact high
Description
Memory safety bugs present in Firefox 116, Firefox ESR 115.1, and Thunderbird 115.1. Some of these bugs showed evidence of memory corruption and we presume that with enough effort some of these could have been exploited to run arbitrary code.
References
-
-
ff v102.15.0 esr
29. aug 2023
Fixed
-
Various security fixes and other quality improvements.
QuoteSecurity Vulnerabilities fixed in Firefox ESR 115.2
- Announced August 29, 2023
- Impact high
- Products Firefox ESR
- Fixed in
-
- Firefox ESR 115.2
#CVE-2023-4573: Memory corruption in IPC CanvasTranslator
- Reporter sonakkbi
- Impact high
Description
When receiving rendering data over IPC
mStreamcould have been destroyed when initialized, which could have led to a use-after-free causing a potentially exploitable crash.References
#CVE-2023-4574: Memory corruption in IPC ColorPickerShownCallback
- Reporter sonakkbi
- Impact high
Description
When creating a callback over IPC for showing the Color Picker window, multiple of the same callbacks could have been created at a time and eventually all simultaneously destroyed as soon as one of the callbacks finished. This could have led to a use-after-free causing a potentially exploitable crash.
References
#CVE-2023-4575: Memory corruption in IPC FilePickerShownCallback
- Reporter sonakkbi
- Impact high
Description
When creating a callback over IPC for showing the File Picker window, multiple of the same callbacks could have been created at a time and eventually all simultaneously destroyed as soon as one of the callbacks finished. This could have led to a use-after-free causing a potentially exploitable crash.
References
#CVE-2023-4576: Integer Overflow in RecordedSourceSurfaceCreation
- Reporter fffvr
- Impact high
Description
On Windows, an integer overflow could occur in
RecordedSourceSurfaceCreationwhich resulted in a heap buffer overflow potentially leaking sensitive data that could have led to a sandbox escape.
This bug only affects Firefox on Windows. Other operating systems are unaffected.References
#CVE-2023-4577: Memory corruption in JIT UpdateRegExpStatics
- Reporter Lukas Bernhard
- Impact high
Description
When
UpdateRegExpStaticsattempted to accessinitialStringHeapit could already have been garbage collected prior to entering the function, which could potentially have led to an exploitable crash.References
#CVE-2023-4051: Full screen notification obscured by file open dialog
- Reporter Hafiizh
- Impact moderate
Description
A website could have obscured the full screen notification by using the file open dialog. This could have led to user confusion and possible spoofing attacks.
References
#CVE-2023-4578: Error reporting methods in SpiderMonkey could have triggered an Out of Memory Exception
- Reporter Irvan Kurniawan (@sourc7)
- Impact moderate
Description
When calling
JS::CheckRegExpSyntaxa Syntax Error could have been set which would end in callingconvertToRuntimeErrorAndClear. A path in the function could attempt to allocate memory when none is available which would have caused a newly created Out of Memory exception to be mishandled as a Syntax Error.References
#CVE-2023-4053: Full screen notification obscured by external program
- Reporter Umar Farooq
- Impact moderate
Description
A website could have obscured the full screen notification by using a URL with a scheme handled by an external program, such as a mailto URL. This could have led to user confusion and possible spoofing attacks.
References
#CVE-2023-4580: Push notifications saved to disk unencrypted
- Reporter Harveer Singh
- Impact moderate
Description
Push notifications stored on disk in private browsing mode were not being encrypted potentially allowing the leak of sensitive information.
References
#CVE-2023-4581: XLL file extensions were downloadable without warnings
- Reporter Umar Farooq (@Puf)
- Impact moderate
Description
Excel
.xlladd-in files did not have a blocklist entry in Firefox's executable blocklist which allowed them to be downloaded without any warning of their potential harm.References
#CVE-2023-4582: Buffer Overflow in WebGL glGetProgramiv
- Reporter Dohyun Lee (@l33d0hyun) of SSD-Disclosure Labs & DNSLab, Korea Univ.
- Impact low
Description
Due to large allocation checks in Angle for glsl shaders being too lenient a buffer overflow could have occured when allocating too much private shader memory on mac OS.
This bug only affects Firefox on macOS. Other operating systems are unaffected.References
#CVE-2023-4583: Browsing Context potentially not cleared when closing Private Window
- Reporter Thejaka Maldeniya
- Impact low
Description
When checking if the Browsing Context had been discarded in
HttpBaseChannel, if the load group was not available then it was assumed to have already been discarded which was not always the case for private channels after the private session had ended.References
#CVE-2023-4584: Memory safety bugs fixed in Firefox 117, Firefox ESR 102.15, Firefox ESR 115.2, Thunderbird 102.15, and Thunderbird 115.2
- Reporter Randell Jesup, Andrew McCreight, the Mozilla Fuzzing Team
- Impact high
Description
Memory safety bugs present in Firefox 116, Firefox ESR 102.14, Firefox ESR 115.1, Thunderbird 102.14, and Thunderbird 115.1. Some of these bugs showed evidence of memory corruption and we presume that with enough effort some of these could have been exploited to run arbitrary code.
References
#CVE-2023-4585: Memory safety bugs fixed in Firefox 117, Firefox ESR 115.2, and Thunderbird 115.2
- ReporterDonal Meehan, Sebastian Hengst, and the Mozilla Fuzzing Team
- Impact high
Description
Memory safety bugs present in Firefox 116, Firefox ESR 115.1, and Thunderbird 115.1. Some of these bugs showed evidence of memory corruption and we presume that with enough effort some of these could have been exploited to run arbitrary code.
References
-
-
ff v117.0
29. aug 2023
New
-
Support for credit card autofill has been extended to users running Firefox in the IT, ES, AT, BE, and PL locales.
-
macOS users can now control the tabability of controls and links via about:preferences.
-
To avoid undesirable outcomes on sites which specify their own behavior when pressing shift+right-click, Firefox now has a
dom.event.contextmenu.shift_suppresses_eventpreference to prevent the context menu from appearing.
Fixed
-
YouTube video lists now scroll correctly when navigating with a screen reader.
-
Various security fixes.
Changed
-
Firefox no longer shows its own screen sharing indicator on Wayland desktop environments. The system default sharing indicator will be used instead.
Enterprise
-
You can find information about policy updates and enterprise specific bug fixes in the Firefox for Enterprise 117 Release Notes.
Developer
-
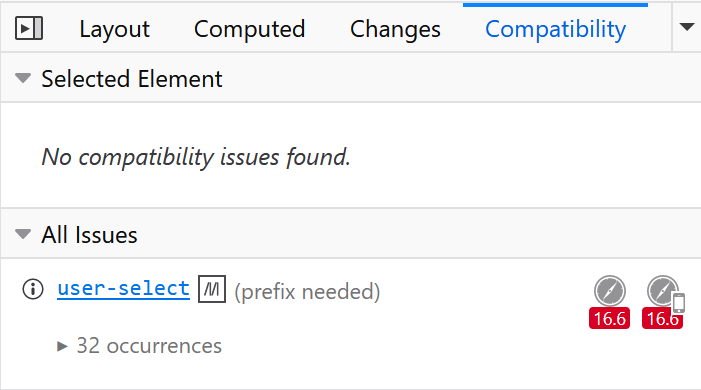
Web compatibility inspection has been enhanced with our new CSS compatibility tooltip in the Developer Tools Inspector. An icon is now displayed next to properties that could lead to web compatibility issues. When hovered, the tooltip indicates which browsers are not supported and displays a link to the MDN page for the property so the user can learn more about it.
-
console.clear()no longer clears the Console output if the "Enable persistent logs" option is enabled.
Web Platform
-
Support for improved CSS nesting is now enabled by default.
-
Firefox now supports
RTCRtpScriptTransform. -
ReadableStream.fromis now supported, allowing creation of a ReadableStream from an (async) iterable. -
Firefox now supports the
math-styleandmath-depthCSS properties and thefont-size: mathvalue.
-
-
ff v116.0.3
16. aug 2023
Fixed
-
Fixed an issue for OPFS users (especially those using the Adobe Photoshop) that broke access to files that were locally cached in a previous version. (bug 1847989, bug 1847619)
-
Fixed an issue that was breaking screensharing for some users on Wayland. (bug 1841851)
-
Fixed an issue where a fullscreen notification was persistently being shown to a user, even after disabling it. (bug 1847901)
-
Fixed an issue where Firefox would hang when doing a Google search. (bug 1847066)
Unresolved
-
A few photoshop users might still encounter issues loading old files which is expected to be resolved in bug 1848916.
-
-
uBOLite v1.0.23.8155
github-actions released this
15. aug 2023
Release notes
- Properly serialize CSS combinators according to position in selector
- Updated filter lists
-
uBOLite v1.0.23.8128
github-actions released this
12. aug 2023
Release notes
This is the first version which functions as expected in Firefox and which is published to AMO.
-
uBOLite v1.0.23.8106
github-actions released this
10. aug 2023
Release notes
- Add managed setting to disable first-run page
- Updated filter lists
-
ublock v1.51.0
github-actions released this
19. jul 2023
Fixes / changes
- Remove obsolete web_accessible_resources
- Add missing (deprecated) method to google ima
-
Fix regression in handling of experimental
header=filter option - Only already normalized CSS selectors can be fast path-compiled
- Improve compatibility with AdGuard's scriptlets
-
Add static network filter option:
permissions -
Add
set-attrscriptlet -
Do not bail too early when trapping properties in
acsscriptlet - Fix regression in cloud storage import of "Filter lists" pane
-
Add
set-session-storage-itemscriptlet - Prevent negative position when widget size is greater than viewport size
- Add visual hint when not all sublists are enabled
-
Add support for AdGuard's noop (
_) network filter option - Add "tabless" filter expression for logger output
-
Add support for logical expressions to
!#ifdirective-
Also added support for
!#else
-
Also added support for
- Add resource aliases for increased compatibility with AdGuard lists
-
Add compatibility with AdGuard's
#%#//scriptlet(...)syntax-
Also added support for quoted parameters in
##+js(...)syntax
-
Also added support for quoted parameters in
- Fix syntax highlighter throwing with invalid patterns
- Prevent creating report until filter lists are updated
- Add support for sublist at any tree depth in "Filter lists" pane
-
Add
set-local-storage-item/trusted-set-local-storage-itemscriptlets -
Fix
m3u-prunescriptlet -
Rework
nowoifscriptlet -
Add
trusted-set-cookiescriptlet (requires trusted source) -
Add
set-cookiescriptlet - Can't have whitespace in network filter pattern
-
-
-
uBOLite v1.0.23.6195
github-actions released this
19. jun 2023
Release notes
- Fix various minor quirks
- Updated filter lists



musik videos
in The Lounge
Posted
karat - der blaue planet (gdr 1982) - a song about the cold war and the danger of a nuklear war
karat - der blaue planet